Responder Field Complete Windows Memory Investigation Suite

CALL FOR SPECIAL GOVERNMENT PRICING
|
 |
Responder™ Field Edition is a complete Windows Memory™ Investigation Suite. This is a must have tool for all computer forensic investigators, law enforcement and information security professionals.
Today, if you’re not doing memory analysis as part of your computer case, you are not doing a complete investigation. Don’t lose your court case because you didn’t perform a complete computer investigation. The Field Edition includes memory preservation, diagnosis and reporting.
Preservation of Windows Physical Memory and Pagefile:
FastDump Pro enables investigators and security analysts to easily "freeze the live memory" on workstations and servers. Pagefile acquisition support, 64-bit support, and FastDump Pro also provide process probing, compression, speed upgrades, and nearly 100% reliable memory-page queries for systems with more than 4GB of RAM.
Memory Analytics:
Responder Field Edition provides the most thorough and comprehensive memory analysis capability in the industry. Responder virtually rebuilds all the underlying data structures in RAM. This includes all physical to virtual address mappings, recreates the object manager, exposes all objects, and enables investigators to perform a complete and comprehensive computer investigation.
Field edition tree view and all processes view:
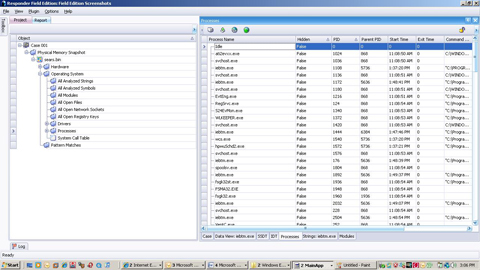
Memory Analysis can expose the following types of information::
Operating System Information:
Running processes
Open files
Network connections and listening ports
Open registry keys per process
Interrupt Descriptor Table
System Service Descriptor Table
Application Information:
Passwords in clear text
Unencrypted data
Instant messenger chat sessions
Document data
Web based email
Outlook email
Malware Detection:
Keystroke logging
Rootkits & Trojans
The HBGary Responder™ platform is designed to perform a comprehensive and complete live Windows memory investigation. Responder allows analysts and investigators to easily preserve the entire contents of live memory and the Pagefile on Windows operating systems in a forensically sound manner. Responder then analyzes and diagnoses the memory image to reveal operating system, user, and application information critical to computer investigations.
Harvested information includes both kernel and user-mode objects, structures, binaries, and other useful artifacts. When malicious or suspect applications, drivers, and other executables are found Responder can seamlessly extract the file(s) from the memory image retaining portable executable (PE) structure so they can be further diagnosed, executed, and monitored in their unpacked state.
This methodology allows Responder to defeat many packers and other obfuscation techniques used by malware writers. Following binary extraction, analysts can utilize Responder’s reverse engineering engine to perform static and runtime disassembly to rapidly identify stealth activity, file system changes, registry modifications, network activity, encryption/decryption routines and other malicious code actions.
Analysts requiring even deeper understanding of malware or suspicious applications can perform binary and runtime forensic analysis with run trace, data flow tracing, and debugging capabilities.
Lots of information can be found in memory, malware, chat sessions, registry keys, encryption keys, socket information and more. Responder™ Professional provides an easy to use GUI that allows you rapid recovery of this type of information. The GUI is designed to support investigation workflow NO DIFFICULT COMMAND LINE interface. Responder allows every investigator to be successful with minimal effort.
| Software License |
$979.00 |
| Annual Maintenance |
$195.00 |